22. Components » Flow Filter¶
The functionality of Wanguard Filter is briefly described in the Choosing a Method of DDoS Mitigation chapter. Flow Filter receives traffic information directly from a Flow Sensor, unlike Packet Filter which needs to inspect every packet in order to extract traffic information.
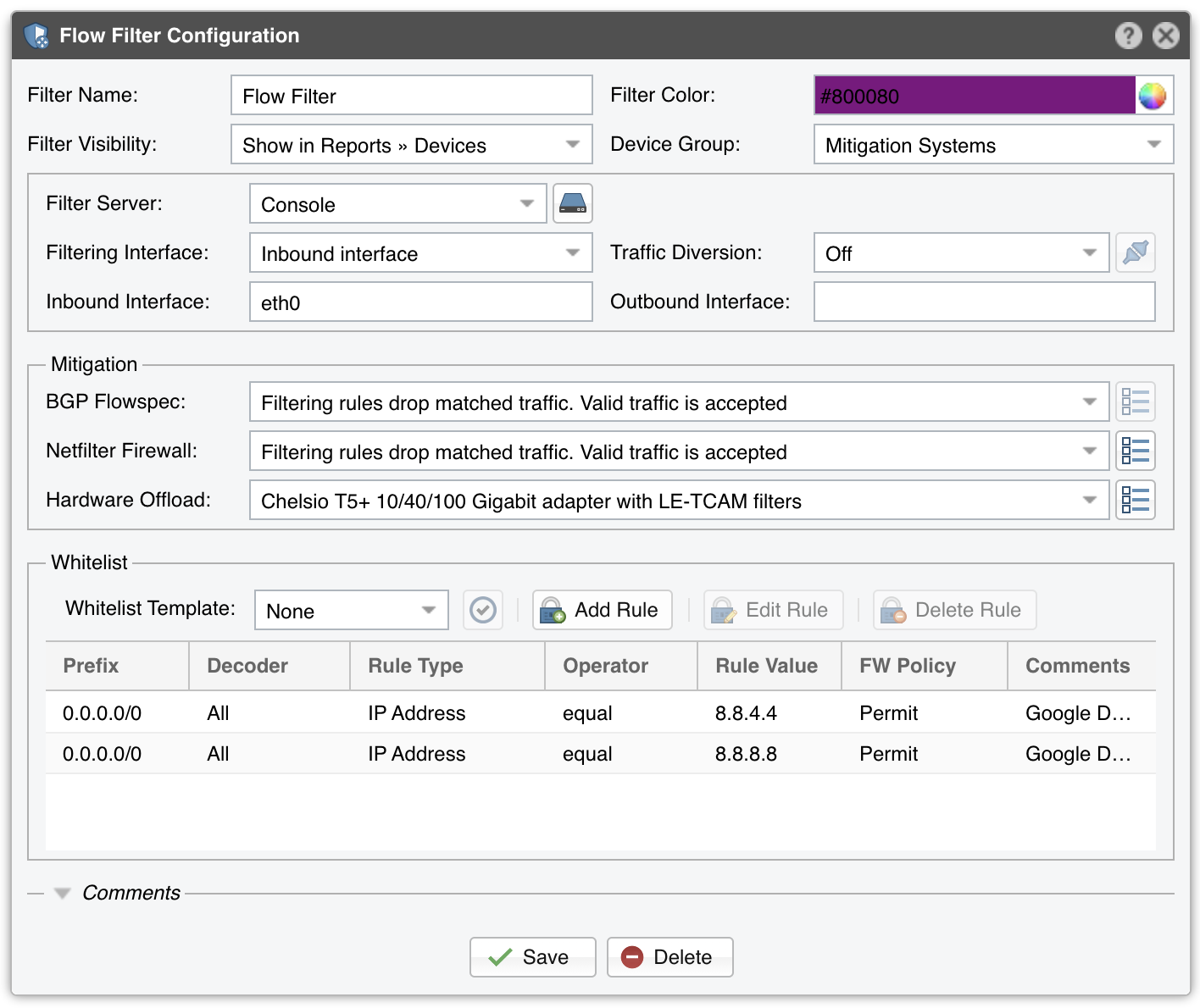
To add a Flow Filter, click the [+] button found in the title bar of the Configuration » Components panel. To configure an existing Flow Filter, go to Configuration » Components and click its name.
Flow Filter Configuration parameters:
● Filter Name – A short name to help you identify the Flow Filter● Filter Color – The color used in graphs for the Flow Filter. The default color is a random one. You can change it from the drop-down menu● Filter Visibility – Toggles the listing inside the Reports » Devices panel● Device Group – Optional parameter used for grouping up components (e.g., by location or role). You can use it to restrict the access of Guest accounts● Filter Server – Select a server that fulfills the minimum system requirements for running the Flow Filter● Filtering Interface – Select where to apply the filtering rules:• None – Flow Filter detects and reports filtering rules, but it doesn’t apply them to a firewalled interface• Inbound interface – Flow Filter applies the filtering rules on the inbound interface, which is defined below• Outbound interface – Flow Filter applies the filtering rules on the outbound interface, which is defined below● Traffic Diversion – Provides a selection of BGP Connectors that can be used for traffic diversion. If the server is deployed inline, or if you do not plan to deploy the server in a Side Filtering topology, leave this parameter set to Off● Inbound Interface – Enter the interface that receives the incoming/ingress traffic. This parameter can be omitted if the Filtering Interface is the same as the Outbound Interface. Bridged interfaces should have the string “physdev:” prepended in front of the interface’s name● Outbound Interface – The cleaned traffic is sent to the downstream router/switch via the outbound interface, which should hold the route to the default gateway. This parameter can be omitted if the Filtering Interface is the same as the Inbound Interface. Bridged interfaces should have the string “physdev:” prepended in front of the interface’s name● BGP Flowspec – Select which policy to apply when the Response is configured to send BGP Flowspec announcements for filtering rules. The rate-limit policy works only for bits/s anomalies; anomalies detected for pkts/s will have the traffic matched by the filtering rule fully discarded● Netfilter Firewall – Flow Filter can use the Netfilter framework included in the Linux kernel to do software-based packet filtering and packet rate limiting. Netfilter is very flexible, and because Flow Filter does not make any use of the connection tracking mechanism specific to stateful firewalls, it is also very fast.• Disabled – Flow Filter detects and reports filtering rules, but the Netfilter firewall API is not used• Filtering rules drop matched traffic. Valid traffic is accepted – Flow Filter detects, reports, and applies filtering rules using the Netfilter firewall. If the filtering rule is not whitelisted, the traffic matched by it is blocked. The remaining traffic is allowed to pass• Filtering rules drop matched traffic. Valid traffic is rate-limited – Flow Filter detects, reports, applies filtering rules and rate-limits the remaining traffic. If the filtering rule is not whitelisted, the traffic matched by it is blocked. The traffic that exceeds the packets/second threshold value is not allowed to pass. Netfilter supports rate-limiting only for packets/s thresholds, not for bits/s thresholds. Also, some kernel versions will fail to rate-limit traffic above 10000 pkts/s and will block all traffic• Filtering rules rate-limit matched traffic. Valid traffic is accepted – Flow Filter detects and reports filtering rules and rate-limits matched traffic to the threshold value. Netfilter supports rate-limiting only for packets/s thresholds, not for bits/s thresholds. Also, some kernel versions will fail to rate-limit traffic above 10000 pkts/s and will block all traffic• Apply the default Netfilter chain policy – Flow Filter detects and reports filtering rules, and applies them to the firewall using the default Netfilter chain policy. The Netfilter framework is still being used, but all rules have the RETURN target. This option is used exclusively for testing and debugging purposes● Netfilter Firewall Options – Click the options button to configure the following additional parameters:• Execution – Filtering rules can be applied automatically without end-user intervention, or manually by an Operator or Administrator that clicks the Netfilter icons in Reports » Tools » Anomalies• Netfilter Table – The raw option requires both Inbound and Outbound interfaces to be set, and it may not work for virtual interfaces. It provides a better packet filtering performance compared to the filter option• Netfilter Chain – Set to FORWARD if the server forwards traffic, or INPUT if it does not• Operating Layer – Set to OSI Layer 2 if the server is configured as a bridge, or OSI Layer 3 otherwise● Hardware Offload – If you have a NIC that provides hardware filters, select the appropriate option. Since hardware filters do not consume CPU, use this feature to complement the Netfilter Firewall and Dataplane Firewall.• Disabled – Hardware filters are not applied• Chelsio T5+ 10/40/100 Gigabit adapter with LE-TCAM filters – Flow Filter uses the cxgbtool utility to apply up to 487 filtering rules that may contain any combination of source/destination IPv4/IPv6 addresses, source/destination UDP/TCP port, and IP protocol. The cxgbtool utility is installed by the Chelsio Unified Wire driver. Drop traffic counters are available for packets, not for bytes• Mellanox ConnectX NIC with OFED driver – Flow Filter uses the /opt/mellanox/ethtool/sbin/ethtool utility to apply up to 924 filtering rules that may contain any combination of source/destination IPv4/IPv6 addresses, source/destination UDP/TCP port, and IP protocol. This utility is installed in the specified path by the OFED driver from Mellanox. Drop traffic counters are not available• Intel x520+ 1/10/40 Gigabit adapter configured to block IPv4 sources – Flow Filter programs the Intel chipset to drop IPv4 addresses from the filtering rules that contain source IPs. Up to 4086 hardware filters can be used. Drop traffic counters are not available• Intel x520+ 1/10/40 Gigabit adapter configured to block IPv4 destinations – Flow Filter programs the Intel chipset to drop IPv4 addresses from the filtering rules that contain destination IPs. Up to 4086 hardware filters can be used. Drop traffic counters are not available● Whitelist – See the dedicated Whitelist Template chapter● Comments – Comments about the Flow Filter can be saved here. These observations are not visible elsewhere
Enable the Flow Filter by clicking the small play/stop button displayed next to its name in Configuration » Components. An instance of the Flow Filter will be launched when a traffic anomaly triggers the Response action “Detect filtering rules and mitigate the attack with Wanguard Filter”. When there is no traffic anomaly that requires its execution, Reports » Devices » Overview will show the “No active instance” message.
To test the firewall configuration, go to Reports » Tools » Firewall and click the [Add Firewall Rule] button.