Company News
IP Monitoring & Anti-DDoS Software Solutions
Andrisoft develops innovative and cost-effective Linux-based applications designed for Network Administrators and Security Experts managing large-scale IP networks, including Telecoms, ISPs, Cloud Hosting Data Centers, CDNs, and DDoS Mitigation Services:
• Wansight delivers bandwidth monitoring, IP accounting and in-depth traffic analysis. It includes a Flow Sensor that analyzes flow records exported via Cisco NetFlow, IPFIX, and sFlow, as well as a Packet Sensor that inspects traffic from in-line deployments, network TAPs, or through port mirroring. A web-based, OS-independent Console provides centralized management and reporting through an intuitive interface.
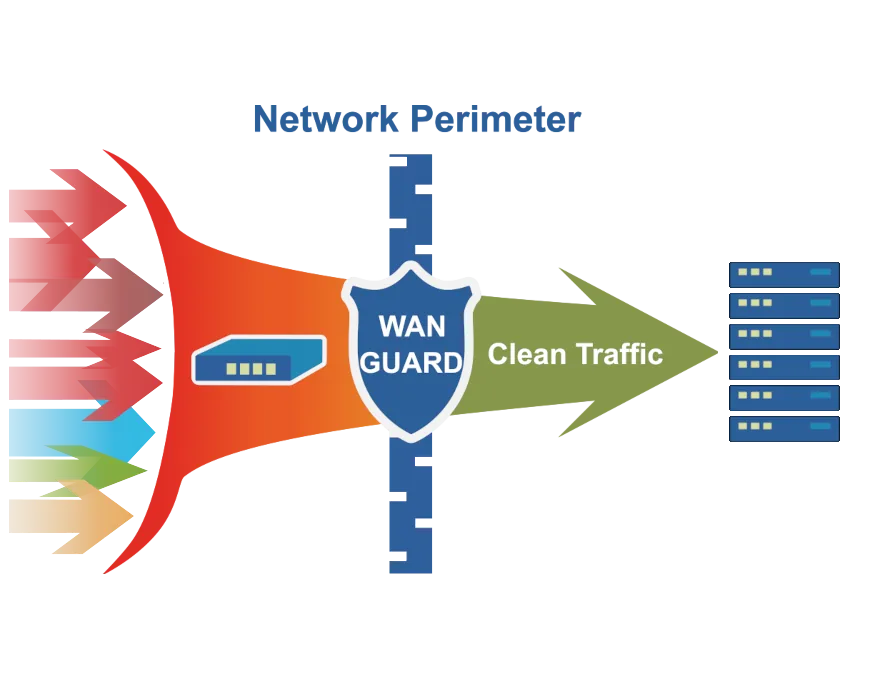
• Wanguard extends Wansight with DDoS detection and DDoS mitigation capabilities. It protects networks and critical services from Distributed Denial of Service attacks by filtering malicious traffic through dynamic rules applied to software or hardware firewalls at the network perimeter. It supports automated response mechanisms, RTBH, BGP Flowspec, traffic diversion, scripting, and clustering for scalable, resilient protection.
DDoS Protection in Five Easy Steps
 1. Discover Wanguard, our solution for monitoring and protecting networks against DDoS attacks.
1. Discover Wanguard, our solution for monitoring and protecting networks against DDoS attacks.
 2. Fill in the evaluation request form in order to receive the download link and a free 30-day trial license key.
2. Fill in the evaluation request form in order to receive the download link and a free 30-day trial license key.
 3. Build your very own DDoS mitigation appliance by installing our software on a spare Linux server.
3. Build your very own DDoS mitigation appliance by installing our software on a spare Linux server.
 4. Use the fully-featured trial version for 30 days. Our engineers will assist you free of charge.
4. Use the fully-featured trial version for 30 days. Our engineers will assist you free of charge.
 5. Buy cost-effective software licenses, at any time, from our online store. The licensing cost also covers support.
5. Buy cost-effective software licenses, at any time, from our online store. The licensing cost also covers support.